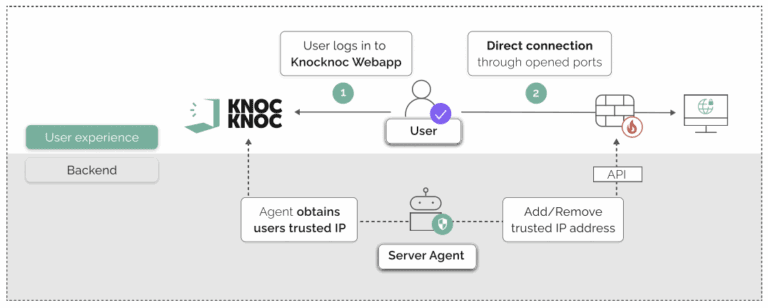
How Knocknoc removes attack surface
Just-in-time, IP-address based network allowlisting.
Simple, very effective and now possible to do at-scale.
Your own infrastructure, fast to deploy without a big project, hosted on-premise – protect internal/external systems at scale.
Make your systems invisible
Knocknoc redefines security by dynamically implementing just-in-time network and application allow-listing. It doesn’t just mitigate risks – it makes attack surfaces disappear.
- Zero day exploitation? Risk removed, or at least greatly reduced.
- Pre-auth exploitation? No longer possible. Attackers can’t reach your systems pre-auth.
- Vulnerability mapping? Prevented, your systems go dark.
- Internal or External? Both. Hide public systems, internal subnets, specific hosts or critical networks.
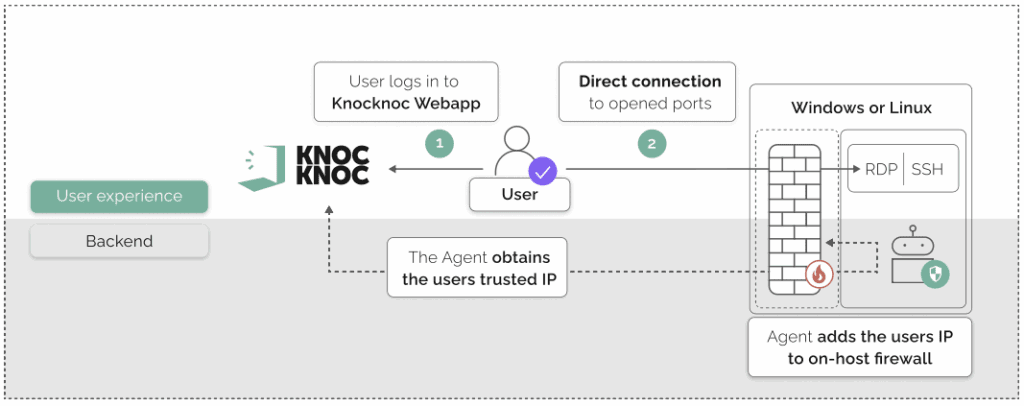
Take a typical SSH bastion host:
- Without Knocknoc: SSH is exposed to the entire internet.
- With Knocknoc: An agent dynamically opens the SSH port only for the authenticated user’s IP address – out of bad. Until then, no port or service is visible.
Network-level exposure is then tied to your IDP – add MFA without changing SSH or interfering with existing, direct network access.
Hide networks, not just hosts, using Knocknoc
Just in time network access
- On premise control: A unique approach to network control infrastructure - novel, elegant, and highly effective.
- Use Your Existing Infrastructure: No additional devices, routes or latency; complete control over direct network access without relying on VPN-like services.
- Timed Access Control: Grant access only when users are authenticated and within predefined timeframes, access management made simple.
Flat internal network? Drop in protection, fast
Flat networks are a fact of life, network segmentation or micro-segmentation can be a big project and requires end-client installation. If you want to protect certain networks or assets fast, Knocknoc can drop in and control pre-authentication attack surface. Think of it as pico-segmentation.
- Knocknoc can be deployed in hours – not days, weeks or months
- No user installation – instant compatibility for unmanaged devices
- Link to your IDP/SAML, use the built-in authentication with MFA or combine them
- Contractor and third-party access – short lived account support
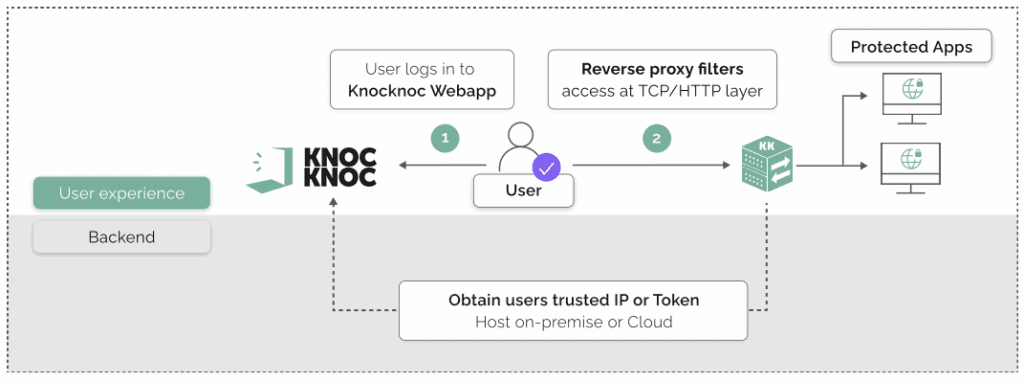
Knocknoc can provide an on-premise control layer with layer-7 filtering for HTTPs URI-level access control, tied to a Knocknoc login
On premise and internal, external and edge, or in public cloud – decentralised and direct network access, all managed centrally